


Cybersecurity (Security+) and P4 Programmable Switches
Monday June 19 – Friday June 23, 2023
- Western Academy Support and Training Center (WASTC)
- University of South Carolina (UofSC)
- Energy Sciences Network (ESnet)
- Online via Zoom
- Link will be published soon
- NetLab link: https://netlab.cec.sc.edu/
Overview
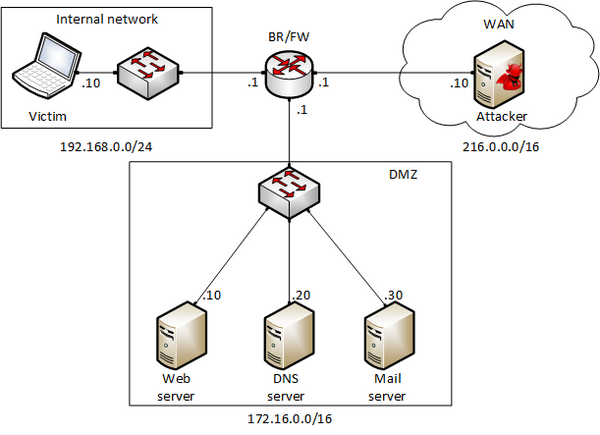
This workshop will cover two virtual lab libraries available for NETLAB+ systems: 1) “Cybersecurity Tools and Applications,” and 2) “P4 Programmable Data Plane Switches.” The “Cybersecurity Tools and Applications” library covers the main concepts needed by learners who may want to be introduced to cybersecurity and/or want to obtain the Security+ certificate. Topics are reinforced with virtual labs that can be deployed in a NETLAB+ system. Examples of labs include Remote Access Trojan (RAT) using Reverse TCP Meterpreter, Social Engineering Attacks, Credentials Harvesting and Remote Access through Phishing Emails, SQL Injection Attack on a Web Application, Cross-site Scripting (XSS) Attack on a Web Application, Asymmetric Encryption (RSA, Digital Signatures, Diffie-Hellman), Configuring a Stateful Packet Filter using iptables, Intrusion Detection and Prevention using Suricata, and more.
The “P4 Programmable Switches” library covers how to write cybersecurity applications targeting programmable data plane switches, thus running at terabits per second (Tbps) rates. These switches have recently emerged and run applications at line rate. Moreover, applications can be reconfigured in the field without additional hardware upgrades, facilitating the deployment of new defenses against unforeseen attacks and vulnerabilities. Examples of labs include Detecting DDoS in the Data Plane, Parsing DNS Packets in P4 Switches and Blocking DNS attacks, Tracking Flows in Real Time, and more.
Outcomes
By the end of this tutorial, attendees will:
Cybersecurity Labs:
- Perform vulnerability scanning and penetration testing
- Create and deploy a malicious payload on a victim's machine
- Maintain persistent access by installing a backdoor
- Perform web-based attacks including SQL injection and XSS
- Understand symmetric and asymmetric cryptography algorithms
- Implement stateful packet filtering and deploying an intrusion detection system.
P4 Security Labs:
- Implement a stateful packet filter for the ICMP and TCP protocols
- Implement a mitigation program for the DNS amplification attack
- Identify and block heavy hitters
- Mitigate Mitigate flood attack
- Mitigate slow DDoS attacks (SlowLoris)
Intended Audience
The tutorial is targeted to IT educators and professionals such as system administrators, network engineers, practitioners. The content is suitable for instructors who want to incorporate advanced material into their networking classes. The content is available for NETLAB systems.
Award Information
This activity is supported by NSF award 2118311. Link to official webpage: NSF-2118311
Pre-requisites
Connectivity to Internet and a browser to access the online virtual platform. Attendees will be provided with an account to access a USC’s NETLAB system: https://netlab.cec.sc.edu/
Agenda
DAY 1: Monday, June 19
| Time (PDT) | Topic | Presenter |
|---|---|---|
| 09:00 - 09:15 | Tutorial Overview | Jorge Crichigno |
| 09:15 - 09:45 | Motivation for Cybersecurity Training [PDF, PPT] | Jorge Crichigno |
| 09:45 - 09:50 | Overview of Cybersecurity Labs [PDF, PPT] | Jorge Crichigno, Elie Kfoury |
| 09:50 - 10:00 | Break | |
| 10:00 - 10:50 | Lab 1: Reconnaissance: Scanning with NMAP, Vulnerability Assessment with OpenVAS [PDF, PPT] | Elie Kfoury |
| 10:50 - 11:00 | Break | |
| 11:00 - 11:50 | Lab 3: Escalating Privileges and Installing a Backdoor [PDF, PPT] | Ali AlSabeh |
| 11:50 - 12:00 | Discussion and Summary Day 1 | Jorge Crichigno |
| 12:00 - 13:00 | Lunch | |
| 13:00 - 14:00 | Office hours | Jorge Crichigno |
DAY 2: Tuesday, June 20
| Time (PDT) | Topic | Presenter |
|---|---|---|
| 09:00 - 09:05 | Review Labs 1, 3 Cybersecurity Lab Series | Jorge Crichigno |
| 09:05 - 09:25 | Social Engineering Attacks [PDF, PPT] | Elie Kfoury |
| 09:25 - 10:15 | Lab 5: Social Engineering Attack: Credentials Harvesting and Remote Access through Phishing Emails [PDF, PPT] | Elie Kfoury |
| 10:15 - 10:25 | Break | |
| 10:25 - 10:45 | Denial of Service (DoS) attacks [PDF, PPT] | Ali AlSabeh |
| 10:45 - 11:45 | Lab 8: Denial of Service (DoS) Attacks: SYN/FIN/RST Flood, Smurf attack, and SlowLoris [PDF, PPT] | Ali AlSabeh |
| 11:45 - 12:00 | Discussion and Summary of Day 2 | Jorge Crichigno |
| 12:00 - 13:00 | Lunch | |
| 13:00 - 14:00 | Office hours | Jorge Crichigno |
DAY 3: Wednesday, June 21
| Time (PDT) | Topic | Presenter |
|---|---|---|
| 09:00 - 09:05 | Review Labs 5, 8 Cybersecurity Lab Series | Jorge Crichigno |
| 09:05 - 09:35 | Stateful Packet Filters and iptables [PDF, PPT] | Ali AlSabeh |
| 09:35 - 10:15 | Lab 12: Configuring a Stateful Packet Filter using iptables [PDF, PPT] | Ali AlSabeh |
| 10:15 - 10:25 | Break | |
| 10:25 - 10:50 | Intrusion Detection and Prevention Systems [PDF, PPT] | Elie Kfoury |
| 10:50 - 11:45 | Lab 14: Intrusion Detection and Prevention using Suricata [PDF, PPT] | Elie Kfoury |
| 11:45 - 12:00 | Discussion and Summary of Day 3 | Jorge Crichigno |
| 12:00 - 13:00 | Lunch | |
| 13:00 - 14:00 | Office hours | Jorge Crichigno |
DAY 4: Thursday June 22
| Time (PDT) | Topic | Presenter |
|---|---|---|
| 09:00 - 09:05 | Review Labs 12, 14 Cybersecurity Lab Series | Jorge Crichigno |
| 09:05 - 09:35 | Motivation for Data Plane Programmability and In-network Defenses [PDF, PPT] | Jorge Crichigno |
| 09:35 - 09:40 | Overview of P4 Security Labs [PDF, PPT] | Jorge Crichigno |
| 09:40 - 10:25 | Lab 5: Introduction to Match-action Tables [PDF, PPT] | Jose Gomez |
| 10:25 - 10:35 | Break | |
| 10:35 - 11:20 | Lab 7: Implementing a Stateful Packet Filter for the TCP protocol [PDF, PPT] | Elie Kfoury |
| 11:20 - 12:00 | Lab 8: Detecting and Mitigating DNS Amplification Attack [PDF, PPT] | Ali AlSabeh |
| 12:00 - 13:00 | Lunch | |
| 13:00 - 14:00 | Office hours | Jorge Crichigno |
DAY 5: Friday, June 23
| Time (PDT) | Topic | Presenter |
|---|---|---|
| 09:00 - 09:05 | Review Labs 5, 7 P4 Security Labs | Jorge Crichigno |
| 09:05 - 09:15 | DDoS Attacks: Heavy Hitters, SYN Flood [PDF, PPT] | Elie Kfoury |
| 09:15 - 10:10 | Lab 9: Identifying Heavy Hitters using Count-min Sketches (CMS) [PDF, PPT] | Elie Kfoury |
| 10:10 - 10:20 | Break | |
| 10:20 - 11:10 | Lab 10: Limiting the Impact of SYN Flood by Probabilistically Dropping Packets [PDF, PPT] | Ali AlSabeh |
| 11:10 - 11:20 | Break | |
| 11:20 - 11:40 | Workshop Summary and Final Discussion | Jorge Crichigno |
| Survey: https://forms.gle/prXRr2jH8Js8c5c5A | ||
Resources
| Item | Note |
|---|---|
| P4 installation guide Link | A useful guide for preparing the environment for P4 development |
| Which open-source IDS? Snort, Suricata or Zeek Link | Study that compares the performance of Zeek, Snort, and Suricata |
| Security Course Slides Link | Slides for a cybersecurity course |
| P4 Cheat Sheet: Link | P4 language cheat sheet |
| BMv2 Docker Containers: Link | DockerHub link for the BMv2 containers |
| Cybertraining Material: Link | List of virtual labs on P4, SDN, network tools and protocols, ... |
| P4 Campus: Link | P4 applications for campus networks |
| FABRIC: Link | A programmable research infrastructure |
| Behavioral Model version 2 (BMv2): Link | Reference P4 software switch used as a tool for developing, testing and debugging P4 data planes |
| Software-Defined Networks: A Systems Approach: Link | A book that explores the key principles of Software-Defined Networking (SDN) |
| Mininet: Link | Virtual testbed enabling the development and testing of network tools and protocols |
| Containernet: Link | Mininet fork that allows to use Docker containers as hosts in emulated networks |
| Mininet Installation:Link | A guide that describes the steps to install Mininet on Linux |
| Wireshark: Link | Packet analyzer used for network troubleshooting, analysis, protocol development, and education |

